VMDR and OEM Cybersecurity in the Automotive Sector
Integrating advanced technologies has propelled vehicles into connectivity and automation in the ever-evolving automotive industry. As Original Equipment Manufacturers (OEMs) continue to innovate and adapt to meet consumer demands, ensuring the security of these connected vehicles has become a paramount concern. One crucial aspect of this endeavour is developing and implementing Vehicle Monitoring, Detection, and Response systems within the automotive cyber security industry. This article will explore how these systems fortify OEM cybersecurity in the automotive sector.
The Evolution of Automotive Cybersecurity
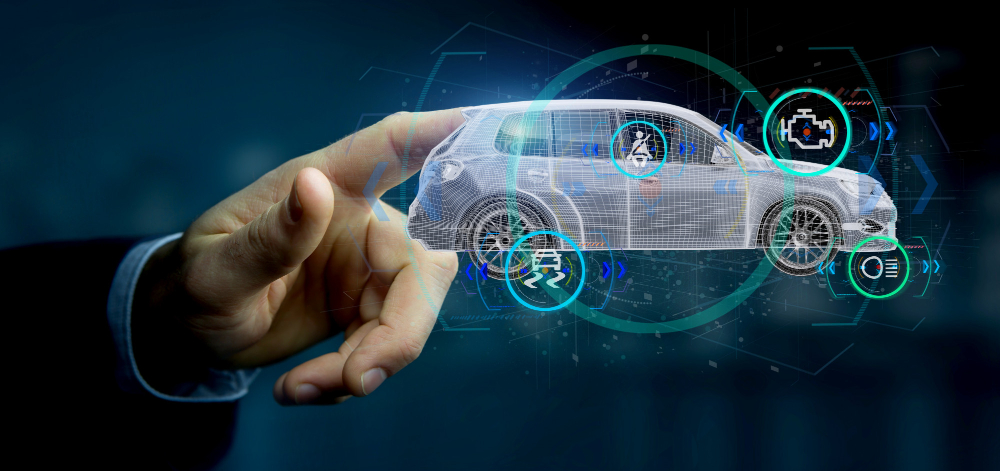
As vehicles become more digitized, they increasingly resemble rolling computers equipped with intricate networks of sensors, software, and connectivity features. These advancements bring convenience and efficiency to drivers but also introduce vulnerabilities. In this context, automotive cybersecurity seeks to protect vehicles from cyber threats that could compromise their safety, data integrity, and functionality.
OEM Cybersecurity: A Top Priority
Original Equipment Manufacturers are at the forefront of addressing these cybersecurity challenges. Recognizing that a breach in their vehicles’ cybersecurity could have far-reaching consequences, OEMs have prioritized cybersecurity. One of the critical components in their arsenal is Vehicle Monitoring, Detection, and Response systems.
Vehicle Monitoring: Eyes on the Digital Road
Vehicle Monitoring is the initial layer of defence in OEM cybersecurity. It involves continuously surveilling a vehicle’s systems, networks, and communications to detect unusual or suspicious activities. This includes:
Network Traffic Analysis: Examining the flow of data within the vehicle’s internal networks and communication with external sources. Any anomalies or deviations from expected patterns are flagged for further investigation.
Behavioural Analysis involves monitoring the behaviour of various vehicle components and software, such as analyzing how the engine management system interacts with other systems and looking for deviations from regular operation.
Data Integrity Checks: Verifying the integrity of data collected by sensors and systems within the vehicle. Any inconsistencies or data corruption can indicate a security breach.
Detection: Identifying the Threats
Once the Vehicle Monitoring system flags a potential anomaly, the Detection phase comes into play. This is where advanced algorithms, machine learning, and artificial intelligence algorithms prove invaluable.
Detection systems can identify a range of cybersecurity threats, including:
Malware: Detection algorithms can identify malicious software in the vehicle’s systems, whether in the infotainment system, engine control unit, or other components.
Unauthorized Access Attempts: Monitoring systems can detect and block unauthorized access attempts to critical vehicle systems, protecting them from tampering.
Abnormal Data Patterns: Detection algorithms can identify unusual data patterns that may indicate a cybersecurity breach or data manipulation.
Response: Swift and Strategic Action
The Response phase is the linchpin in the cybersecurity process. When a threat is detected, swift and strategic action is essential to mitigate potential harm.
OEMs have established response protocols that include:
Isolation: If a breach is detected, the affected systems can be isolated from the network to prevent further damage and protect other critical vehicle functions.
Patch Deployment: Security patches and updates can be deployed remotely to address vulnerabilities and close security gaps.
Incident Investigation: Following an incident, OEMs conduct thorough investigations to understand the scope and nature of the breach, helping to prevent future attacks.
Regulatory Compliance: Compliance with automotive cybersecurity regulations and standards is maintained, with incidents reported as necessary to regulatory authorities.
Collaboration and Continuous Improvement
OEMs understand that automotive cybersecurity is not a one-time effort but an ongoing process. Collaborative efforts with cybersecurity experts, industry organizations, and government bodies are vital in staying ahead of emerging threats. Regularly updating and enhancing vehicle monitoring, detection, and response systems is essential to adapting to evolving cyber risks.
As vehicles become increasingly connected and reliant on digital systems, OEM cybersecurity in the automotive industry has never been more critical. Vehicle Monitoring, Detection, and Response systems are pivotal components of this cybersecurity framework, ensuring that threats are identified and addressed swiftly.
OEMs are committed to safeguarding their vehicles and the data they collect from cyber threats, enhancing consumers’ safety and privacy. With continuous improvement, collaboration, and adherence to cybersecurity standards, the automotive industry is well-positioned to meet the challenges of an ever-evolving digital landscape and provide secure and reliable transportation for the future.