Emerging Technologies and Their Impact on Business Security
- 1 Impact of Emerging Technologies on Business Security
- 1.1 The Cascade of Proliferating Data Streams
- 1.2 The Cloud: A Haven or a Storm?
- 1.3 Artificial Intelligence: A Double-Edged Sword
- 1.4 Decentralization: The Crux of Security and Trust
- 1.5 Emerging Defences in a Digital Age
- 1.6 Evolving Strategies in Cybersecurity
- 1.7 Humanizing the Security Equation
- 1.8 Future-Proofing Business Security
- 2 Conclusion:
- 2.1 FAQs:
- 2.1.1 How do businesses balance the benefits of IoT with security concerns?
- 2.1.2 What are the key challenges in securing data stored in the cloud?
- 2.1.3 How can businesses harness the power of AI while mitigating security risks?
- 2.1.4 What are the benefits and challenges of decentralized technologies like blockchain for business security?
- 2.1.5 What is the zero-trust model, and how does it enhance cybersecurity?
- 2.1.6 What is privacy-enhancing computation, and how does it address privacy concerns in data processing?
- 2.1.7 Why is humanizing security crucial in the digital age?
In Short:
- Data Deluge and IoT Vulnerabilities: Emerging technologies amplify data streams, raising concerns about securing interconnected IoT devices and respecting individual privacy rights.
- Cloud Computing Challenges: Cloud adoption offers scalability but requires robust security measures to mitigate risks such as data breaches and compromised credentials.
- AI and Decentralization Duality: Artificial intelligence accelerates threat detection but also empowers adversaries, while decentralized technologies like blockchain offer enhanced security alongside new challenges.
In the rapid-fire trajectory of technological advances, businesses are experiencing both burgeoning opportunities and unprecedented challenges. Emerging technologies – from artificial intelligence to the Internet of Things – have rewritten the playbook for business operations, customer engagement, and competition strategy. Yet, the glowing ember of opportunity is often fanned by the winds of vulnerability, especially regarding security.
As we witness the evolution of transformative technology, we also find ourselves embroiled in an arms race against cyber threats that evolve alongside these innovations. Navigating the labyrinth of potential security pitfalls has become a core business strategy that demands agility, foresight, and a touch of humanity.
Impact of Emerging Technologies on Business Security
The Cascade of Proliferating Data Streams

We live in a world awash with data, with every click, swipe, and interaction funnelling into a tidal wave of information. Emerging technologies amplify these streams, enabling vast data collection, analysis, and leverage in real time. But where opportunity flows, risk follows in its wake. Businesses are now custodians of a data trove so immense that any breach can lead to significant reputational and financial damage.
A prime concern is the security of the Internet of Things (IoT), a sprawling web of interconnected devices that exchange data continuously. Each device, from the seemingly innocuous office thermostat to the integral smart factory sensor, opens a doorway that cybercriminals could exploit. The question businesses face is how to secure these countless nodes and how to do so in a manner that respects the individual’s right to privacy and trust.
The Cloud: A Haven or a Storm?
Emerging technologies have steered us towards the beckoning horizon of cloud computing, a domain where scalability and flexibility reign supreme. The cloud’s omnipresence has dissolved traditional perimeters, as data now traverses global, shared infrastructures. The ease with which we access and store data in the cloud carries an undercurrent of risk with the potential for data breaches, service disruptions, and compromised credentials.
To navigate these tumultuous skies, businesses must implement robust security measures, such as advanced encryption, stringent access controls, and ongoing vulnerability assessments. Yet, equally important is the human element: fostering a culture where security consciousness is as habitual and intuitive as checking the weather before heading out into the storm.
Artificial Intelligence: A Double-Edged Sword

Artificial intelligence and machine learning present a bold new frontier that can autonomously detect and respond to security incidents much faster than human capabilities allow. However, these same technologies can embolden adversaries, enabling sophisticated, adaptive attacks that can learn from and evade traditional defences.
Here lies the imperative for businesses to humanize AI-driven security, blending algorithmic precision with human oversight and ethical considerations. AI must not simply be a tool wielded but a collaborative partner, informed by the values and discernment of those it serves.
Decentralization: The Crux of Security and Trust
Decentralized technologies like blockchain have entered the business vocabulary with promises of immutable records and enhanced security. Yet, while these technologies offer a bastion against certain types of attacks, they also present novel challenges, such as code vulnerabilities in smart contracts or the integrity of the consensus mechanisms.
In this brave new world of decentralization, the security of a blockchain-based system is only as robust as the human intellect that crafts its smart contracts and the collective vigilance that guards its operations.
Emerging Defences in a Digital Age
In retaliation to these emerging threats, pioneering security measures crystallize within the digital tapestry. For instance, concepts such as GoProxies denote advanced security solutions that offer businesses a means to cloak their digital footprints, shielding sensitive operations from the prying eyes of malevolent actors.
The beauty of such defences does not lie solely in their technical prowess but also in their embodiment of human ingenuity and foresight – a testament to our adaptive spirit.
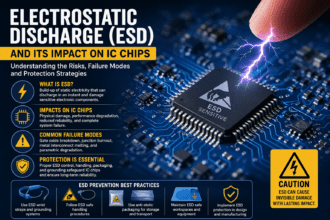
Evolving Strategies in Cybersecurity
![]()
Today’s businesses are required to adopt a more fluid, comprehensive approach to security. This necessitates an architectural transformation towards a ‘cybersecurity mesh’, where security parameters extend beyond fixed locations to encompass individual access points bolstered by adaptable identity and access management.
The zero-trust model is at the forefront of this movement. It is a doctrine that eschews inherent trust in favour of relentless verification. It democratizes security within the corporate structure, mandating that all users, irrespective of their rank or location, prove their legitimacy.
Another beacon of hope is the burgeoning field of privacy-enhancing computation (PEC), which enables the processing and analysis of data without exposing it. Techniques such as confidential computing and secure multiparty computation forge a path forward where privacy can coexist with big data and analytics ambitions.
Humanizing the Security Equation
While emerging technologies shape the tools we have at our disposal, the human factor ultimately dictates their success. Bridging the gap between technology and its users is the crucial ingredient often neglected in the discourse on security.
Educating, empowering, and engaging the workforce in security best practices transforms employees from potential liabilities into proactive guardians of the digital domain. Humanizing security also means recognizing the customer’s voice, addressing their privacy concerns, and building a brand synonymous with trust and integrity.
Future-Proofing Business Security
Looking ahead requires businesses to parse the complex interplay between emerging technologies and security cautiously and enthusiastically. Business leaders must inoculate their organizations through continuous vigilance, astute investment, and an unwavering commitment to infusing human insight into an evermore automated environment.
The result is a delicate dance between embracing technological innovation and fortifying against the shadows it may cast. Businesses stand at the helm, guiding their vessels through these waters with a steady hand, knowing that their precious cargo – data, reputation, and customer trust – must be guarded with the synergy of technology and humanity.
Security is not simply about building walls and moats in the digital realm; it is about creating ecosystems where trust permeates every interaction and innovation is pursued without sacrificing the sanctity of security. The emerging technologies of our times offer incredible vistas of potential. Still, the human touch will ensure we navigate this new era not merely with caution but with confidence and grace.
Conclusion:
In navigating the evolving landscape of emerging technologies, businesses must prioritize security measures that blend technical prowess with human insight. By fostering a culture of security consciousness, embracing innovative defences, and humanizing security strategies, organizations can navigate the complexities of this digital era with confidence and grace.
FAQs:
How do businesses balance the benefits of IoT with security concerns?
Businesses must implement robust security measures for IoT devices, including encryption and access controls, while respecting individual privacy rights.
What are the key challenges in securing data stored in the cloud?
Cloud computing introduces risks such as data breaches and compromised credentials, necessitating advanced encryption and ongoing vulnerability assessments.
How can businesses harness the power of AI while mitigating security risks?
Businesses should humanize AI-driven security by blending algorithmic precision with human oversight and ethical considerations.
What are the benefits and challenges of decentralized technologies like blockchain for business security?
Blockchain offers enhanced security through immutable records but presents challenges such as code vulnerabilities and consensus mechanism integrity.
What is the zero-trust model, and how does it enhance cybersecurity?
The zero-trust model mandates relentless verification for all users, democratizing security within the corporate structure and minimizing inherent trust.
What is privacy-enhancing computation, and how does it address privacy concerns in data processing?
Privacy-enhancing computation techniques like confidential computing enable data processing and analysis without exposing sensitive information.
Why is humanizing security crucial in the digital age?
Bridging the gap between technology and users through education and empowerment transforms employees into proactive guardians of the digital domain, ensuring a culture of security consciousness.