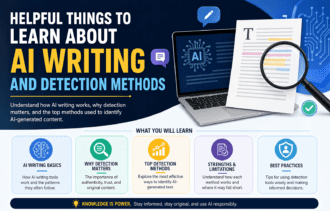
The Growing Threat of AI-Powered Cyber Attacks
In the swiftly evolving landscape of cybersecurity, particularly in the AI Era, the importance of Data Loss Prevention (DLP) has never been more pronounced. The integration of artificial intelligence (AI) marks a significant paradigm shift in this field. Once predominantly a tool wielded by defenders to identify and thwart cyber threats, AI is now increasingly viewed as a double-edged sword. While its sophistication is a boon for security measures, it also empowers malicious actors to engineer more complex and covert cyber attacks.
This article delves into the escalating threat of AI-powered cyber attacks, unraveling the complexities of this new battleground in the digital world. It also provides first insights on Data Loss Prevention for the AI Era strategies that must evolve to navigate this ever-changing landscape effectively.
The Evolution of AI in Cybersecurity

The integration of AI in cybersecurity heralds back to its initial use as a defensive mechanism. In its nascent stages, AI was harnessed to detect patterns and anomalies in data, serving as a vigilant guard against traditional cyber threats. This period witnessed the emergence of AI-powered tools capable of real-time threat detection, predictive analysis, and automated responses to security incidents. These advancements significantly boosted the defense capabilities of organizations, providing them with a robust shield against the ever-evolving nature of cyber threats.
AI in the Hands of Attackers

The rapid advancements in artificial intelligence have undeniably transformed various aspects of our lives, bringing efficiency and innovation. However, these advancements have also led to a significant and concerning development in the world of cyber threats. The emergence of AI tools in the arsenal of cyber attackers marks the beginning of a new and more daunting era in the cyber threat landscape, akin to opening Pandora’s box, unleashing a host of new challenges.
The integration of AI into cyber attacks represents a leap in the sophistication and complexity of these threats. Attackers are now leveraging AI to automate the process of discovering vulnerabilities within digital systems. This automation goes beyond traditional methods, allowing cybercriminals to identify and exploit weaknesses at an unprecedented scale and speed. The capabilities of AI enable these attackers to orchestrate complex and large-scale attacks, which are not only more efficient but also significantly harder to trace and counter.
Furthermore, one of the most alarming aspects of AI in cyber attacks is its ability to mimic normal user behavior. By doing so, these AI-driven threats can evade detection for longer periods, seamlessly blending in with legitimate activities. This cunning strategy poses a formidable challenge to traditional security protocols, which are primarily designed to identify and block overtly malicious activities.
This paradigm shift in the nature of cyber threats necessitates a critical re-evaluation and adaptation of defense strategies. In the age of AI-powered cyber warfare, it is no longer sufficient to rely on conventional cybersecurity measures. The defense mechanisms must evolve to be as dynamic and intelligent as the threats they are designed to combat. This involves not only upgrading technological defenses but also rethinking the approach to cybersecurity, emphasizing proactive threat detection and adaptive response strategies.
The advent of AI in the hands of cyber attackers is a game-changer, introducing a level of complexity and danger that was previously unimagined. As these AI-powered threats become more sophisticated, the need for equally advanced and innovative defense strategies becomes paramount to protect digital infrastructures and ensure cybersecurity in this new era.
Understanding the Risks
Let’s highlight the escalating threat posed by AI-powered cyber attacks, emphasizing their sophistication, speed, adaptability and other risks.
AI algorithms are designed to handle complex tasks with greater efficiency than traditional methods. In the context of cyber attacks, this means these algorithms can execute attacks that are intricate and harder to detect. They can find and exploit loopholes that might be overlooked by human hackers or conventional software.
AI systems can process vast amounts of data at speeds far beyond human capabilities. This speed allows AI-driven cyber attacks to adapt quickly to changing environments and defenses. They can analyze the responses of security systems in real-time and modify their strategies instantaneously, making them more difficult to combat.
One of the key strengths of AI is its ability to sift through and analyze large datasets quickly. In cyber attacks, AI can use this capability to scan for vulnerabilities in a system. This is not limited to known vulnerabilities; AI can also potentially identify unknown weaknesses, exploiting them before they are patched.
AI enables a higher degree of personalization and precision in cyber attacks. By analyzing data about a target, AI can customize the attack to be more effective, whether it’s targeting a specific organization, infrastructure, or even an individual.
Traditional cybersecurity defenses are often rule-based or pattern-based, designed to detect known threats. However, the dynamic nature of AI-powered attacks can bypass these measures, as AI can continuously learn and adjust its methods to avoid detection.
The risks associated with these attacks are varied and significant. Financial losses from data theft or business disruption are immediate concerns. Data breaches can compromise sensitive personal and corporate information. Beyond this, the potential impact on critical infrastructure (like power grids or transportation systems) and national security is profound, with long-term and far-reaching consequences.
Traditional cyber attacks might be one-off or require sustained input from the attackers. In contrast, AI can enable continuous, automated attacks without direct human oversight. This means that an AI-driven attack can persist over a longer period, constantly probing and attacking a target, which significantly raises the stakes in cybersecurity.
The landscape of cyber warfare is changing, with AI at the forefront, necessitating a proactive and innovative approach to cybersecurity.
Strategies for Defense

In the ever-evolving world of cybersecurity, defending against AI-powered threats is a complex challenge. Organizations need to be proactive and innovative in their approach to safeguard their digital assets and data against these sophisticated threats.
What can you do:
- Invest in Advanced AI Security: Implement AI systems for proactive threat identification and neutralization.
- Cultivate Security Awareness: Train staff regularly on cybersecurity and emerging threats.
- Foster Cross-Sector Collaboration: Work with industry, academia, and government for comprehensive defense strategies.
- Stay Informed of Cyber Trends: Continuously monitor and adapt to new cyber threats.
The Future of AI in Cybersecurity
As we peer into the future of AI in cybersecurity, it becomes evident that this field will continue to evolve rapidly. AI’s role is expected to expand, not just in defensive mechanisms, but also in its use by cyber attackers, necessitating an ongoing and dynamic adaptation in security strategies. This evolution underscores the need for continuous research and development in cybersecurity, ensuring that defense mechanisms remain a step ahead of attackers. The future of cybersecurity, intertwined with AI, demands vigilance and innovation, as the digital landscape remains an ever-changing frontier of challenges and opportunities.